You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
VaultWiki [Paid] 4.1.7 Patch Level 1
No permission to buy ($15.00)
- Thread starter pegasus
- Start date
It's a little bit strange : you was hacked on 9.1 , but on 20.1 you post the info
In 20.1 he found out that his site was hacked ? Ah ok . ThxHe just found out.
Version control does not show any unauthorized or unintended changes to the package between 1/9 and 1/20. We will regenerate cached versions of the package today.We need an audit of the download package.
If you updated your VaultWiki installation between these dates, you may just want to run XenForo's File Health Check to be safe (AdminCP > Tools > Diagnostics > File Health Check).
Last edited:
Version control does not show any unauthorized or unintended changes to the package between 1/9 and 1/20. We will regenerate cached versions of the package today.
If you updated your VaultWiki installation between these dates, you may just want to run XenForo's File Health Check to be safe (AdminCP > Tools > Diagnostics > File Health Check).
Done . I have these 3 Files
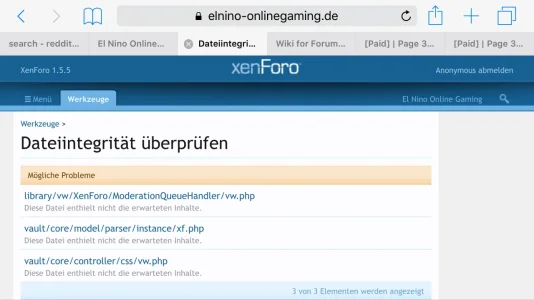
It may be due to bug fixes that were applied on your site. You can ZIP the files and send them to support@vaultwiki.org to have them looked at.
Ok . I will Send you the files , when I at home.
I think that how you have told your userbase everything about the hack should be commended. Not many businesses follow this openness with their customers. Many could learn a thing or two. I commend you.VaultWiki.org was recently hacked. If you have an account at the site, you will want to read the disclosure: https://www.vaultwiki.org/articles/183/
You can look on my site https://www.elnino-onlinegaming.de/wiki
I've had VaultWiki up for a long while now (Like 2-3 months) and it JUST went down. http://rpgmakermv.co/wiki_index/ gives me a
This webpage has a redirect loop
ERR_TOO_MANY_REDIRECTS
Out of no where.
This webpage has a redirect loop
ERR_TOO_MANY_REDIRECTS
Out of no where.
Have you changed any VaultWiki settings lately or did you change XenForo's friendly URLs setting? It is unlikely that you would suddenly get a redirect loop if nothing has changed.
Go to Admin > Wiki > Maintenance > Rebuild Counters / Caches > Rebuild Content URLs.
If that does not work and you don't know what was changed on your site, you may have to request ticket support from the VaultWiki site.
Go to Admin > Wiki > Maintenance > Rebuild Counters / Caches > Rebuild Content URLs.
If that does not work and you don't know what was changed on your site, you may have to request ticket support from the VaultWiki site.
The error in the screenshot suggests that a required file is missing (but you would not have gotten that far if it was), or that the POST 'counter' value does not correspond to any of the counter builders in VaultWiki.
It is possible that another add-on is filling the POST 'counter' = 'url' value with something else. Try disabling other add-ons that you installed since installing VaultWiki, and see if you regain the ability to use this form.
If not, you will need to submit a ticket at VaultWiki.org, so that they can investigate how that value is being filled on your site.
It is possible that another add-on is filling the POST 'counter' = 'url' value with something else. Try disabling other add-ons that you installed since installing VaultWiki, and see if you regain the ability to use this form.
If not, you will need to submit a ticket at VaultWiki.org, so that they can investigate how that value is being filled on your site.
Last edited:
pegasus updated VaultWiki with a new update entry:
Changes in 4.0.8
Read the rest of this update entry...
Changes in 4.0.8
(released December 24, 2015)
- Style Properties for History Status Colors
- Fixed instant emails for edits to same subscribed page
- Fixed email notifications for feed updates
- Fixed feed entries not removed when feed is deleted
- Fixed E_NOTICE errors still halt install/upgrade with debug off
- Fixed invalid closing tags in wiki prefs
- Fixed array to string conversion editing comments
- Fixed fatal error upgrading to 4.0.6 from 4.0.0 Beta 7
- Fixed can't chmod existing CSS...
Read the rest of this update entry...
is the new version not 4-0-9
i have some error in the version 4-0-8
i have some error in the version 4-0-8
pegasus updated VaultWiki with a new update entry:
Changes in 4.0.9
Read the rest of this update entry...
Changes in 4.0.9
(released March 2, 2016)
- Compatibility with [bd] WidgetFramework 2.6+
- missing data in VW4 import
- missing data in VW3 import
- upgrade might skip number of steps from previous upgrade
- tweaked responsive style on some pages
- can't approve moderated discussions
- broken images using FILE for non-images
- add-on upgrade control doesn't redirect to upgrade script
- no available target area for non-normal page when area only accepts that kind
- extra queries when pages...
Read the rest of this update entry...
Similar threads
- Replies
- 1
- Views
- 45
- Replies
- 3
- Views
- 54