- Compatible XF 1.x versions
- 1.4
- 1.5
- Additional requirements
- php 5.4+
- License
- MIT License
- Visible branding
- No
Password Tools
Description
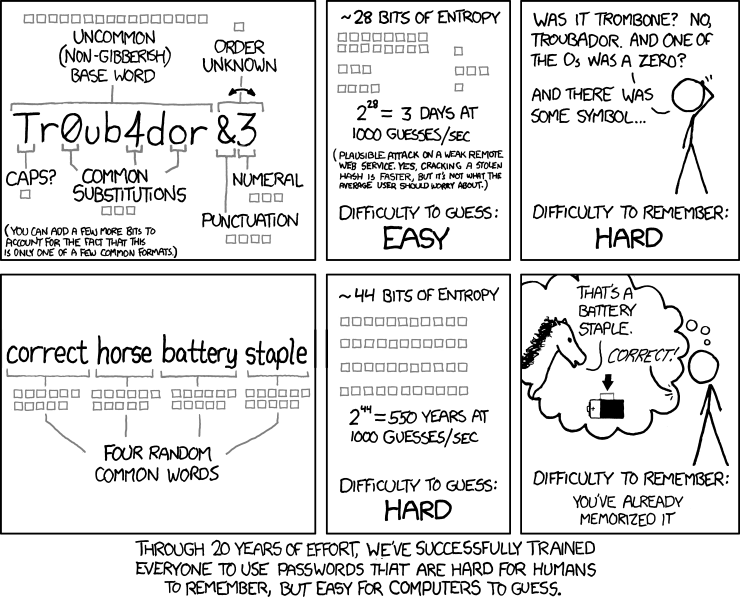
This modification mostly follows the principles of Dan Wheelers password strength estimator zxcvbn. It does not weight password strength by their combination of upper/lower letters, special characters and numbers, but on how easy they are to crack in reality.
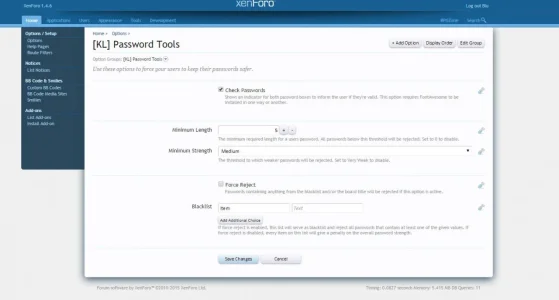
To increase the safety of your users account, you can force them to use passwords of a minimum length, minimum strength and even force them to exclude certain words from their passwords (like your site name, the topic your site refers to, etc.).
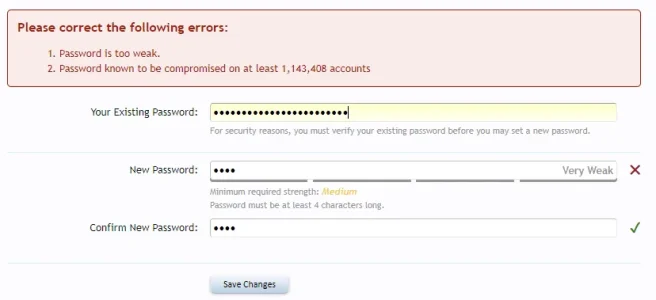
But the other side of the equation, is no matter how secure the password is, if it has been compromised not password strength estimator will help make it better. As such NIST has the following guidance: check passwords against those obtained from previous data breaches. Pwned Password integration does that.
Features


Installation
I recommend using Add-on install & upgrade to install this add-on.
Description
This modification mostly follows the principles of Dan Wheelers password strength estimator zxcvbn. It does not weight password strength by their combination of upper/lower letters, special characters and numbers, but on how easy they are to crack in reality.
To increase the safety of your users account, you can force them to use passwords of a minimum length, minimum strength and even force them to exclude certain words from their passwords (like your site name, the topic your site refers to, etc.).
But the other side of the equation, is no matter how secure the password is, if it has been compromised not password strength estimator will help make it better. As such NIST has the following guidance: check passwords against those obtained from previous data breaches. Pwned Password integration does that.
zxcvbn Readme said:
Thanks @WoodiE for funding the HIBP (pwned password) integration.Pwned password said:
Features
- Show users how strong their passwords really are when it comes to crack-attempts
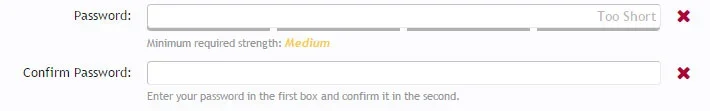
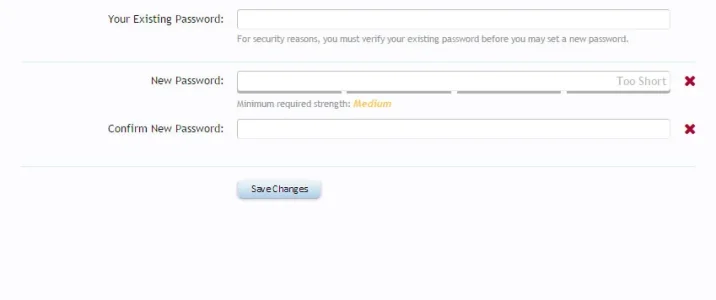
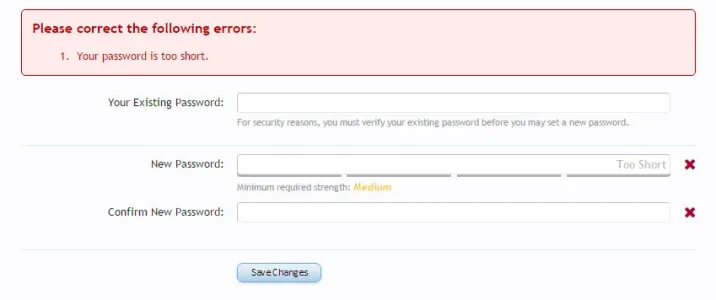
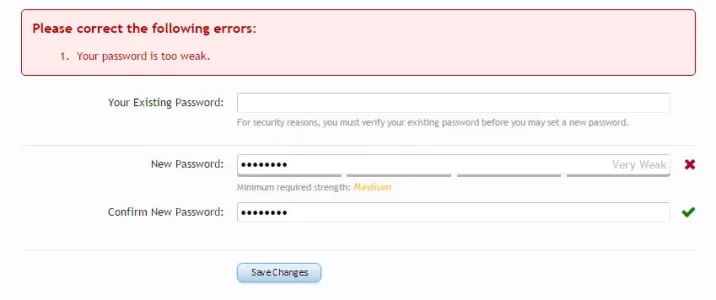
- Deliver instant feedback if password and password-confirm match and/or certain requirements are not met
- Force users to choose passwords with a minimum strength
- Force users to choose passwords with a minimum length
- Force users to chooce a password not containing words from a blacklist you define
- No cheating: This modification also controls users passwords on server side with Ben Jeavos php-implementation of zxcvbn.
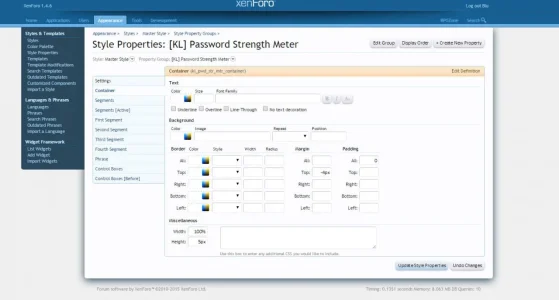
- Easy styling through XenForo Style Properties
Installation
I recommend using Add-on install & upgrade to install this add-on.
- Related resources