@Xon
it is really helpful to have this
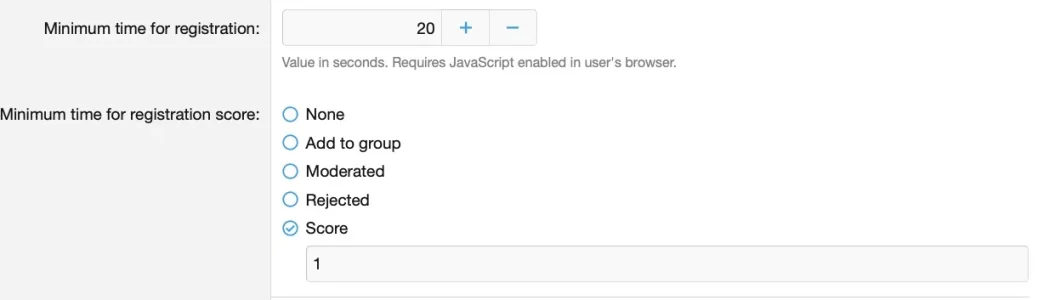
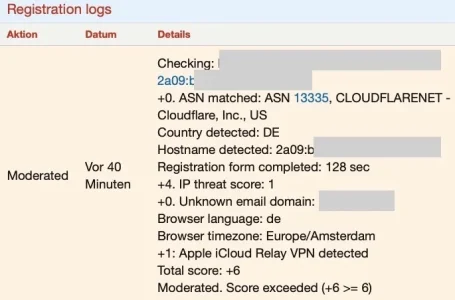
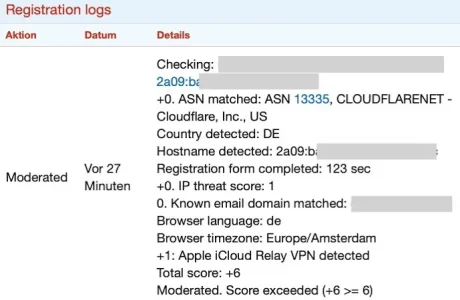
Users that come over Apple private relay on my forums typically come either via the Cloudflare ASN or via the Akamai ASN. Akamai does have a way higher scoring (4) than Cloudflare (1) - i think both are defaults. Now, instead of overruling the scoring of the ASN in question the value for Apple private relay is added on top of that, making it a especially bad offender and sending users with Apple private relay safely into moderation.
Is this the intention? Wouldn't it be a better solution to override the score for the underlying ASN and to replace it with whatever one sets as score for Apple private relay?
it is really helpful to have this
- Add Apple Relay detection for registration spam detection (default enable, with a score of 3)
Users that come over Apple private relay on my forums typically come either via the Cloudflare ASN or via the Akamai ASN. Akamai does have a way higher scoring (4) than Cloudflare (1) - i think both are defaults. Now, instead of overruling the scoring of the ASN in question the value for Apple private relay is added on top of that, making it a especially bad offender and sending users with Apple private relay safely into moderation.
Is this the intention? Wouldn't it be a better solution to override the score for the underlying ASN and to replace it with whatever one sets as score for Apple private relay?