You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
[TH] Install and Upgrade [Deleted]
- Thread starter Jon W
- Start date
Just checked (look at me being all helpfulIf the password is actually being printed back out, it would be in the page source; inspecting it may not show as a browser design choice. I don't know the implementation to know whether or not that's the case though.
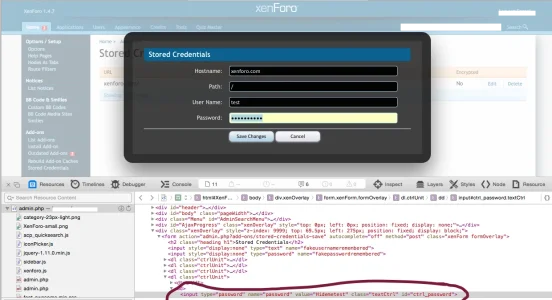
I was the one who noticed it. I can still reproduce this in safari, by clicking on the "stored credentials" option in ACP, clicking edit on the desired credential and then right clicking in the password field and inspecting. In the screenshot, you can see username is test and password is "hidemetest". Not major if you are the only admin with ACP access but unsafe if you aren't.
Attachments
Okay, I didn't have the whole edit the field first part of the equationI was the one who noticed it. I can still reproduce this in safari, by clicking on the "stored credentials" option in ACP, clicking edit on the desired credential and then right clicking in the password field and inspecting. In the screenshot, you can see username is test and password is "hidemetest". Not major if you are the only admin with ACP access but unsafe if you aren't.
Yes, I can confirm this.
Anyone with the premium version that can test as well? I know it says you can enable encryption of the password in the database with the premium version but wondering if it still shows in the ACP using this method.
Yeah, sorry. I wasn't as clear about the procedure when @Brogan and myself were talking about it.Okay, I didn't have the whole edit the field first part of the equation
Yes, I can confirm this.
@jOOc,I have the latest versions of these two add-on's but they still shows up as outdated, why?
View attachment 106729
Did you find a solution? I am having the same issue with 2 different mods.
Thanks.
Jon W
Well-known member
Jon W updated Install and Upgrade by Waindigo with a new update entry:
Version 1.4.10 released
Read the rest of this update entry...
Version 1.4.10 released
Bug fixes:
- Fixes outdated add-ons counter in XenForo 1.5 Beta 1.
Read the rest of this update entry...
Hi, I tried to download your addon, but keep getting this message from Chrome:
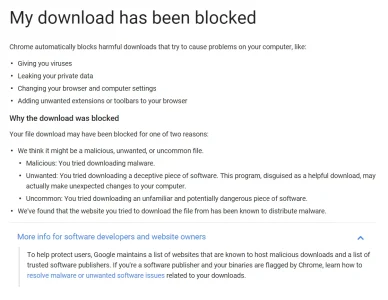
They give this link for help:
Malware and unwanted software - Search Console Help
Hope this helps,
Andre
They give this link for help:
Malware and unwanted software - Search Console Help
Hope this helps,
Andre
@TDUBS It hasn't been fixed.
Thank you. I disabled the addon until it's fixed.
@TDUBS However you can prevent the Stored Credentials page to return the actual password when someone tries to edit it by editing this file:
On my case, I added this line:
The function that returns the password begins on line 497 (function name: actionStoredCredentialsEdit). Preventing the function from returning the actual password should be enough if all you worry about is other admins that have access to Admin CP from accessing the password.library\Waindigo\InstallUpgrade\Extend\XenForo\ControllerAdmin\AddOn.php
On my case, I added this line:
right before this line (adding it after will also work - just make sure it's changed before being added to $viewParams array):$credential['password'] = "fake password";
$credential = $installUpgradeModel->prepareCredential($credential);
Last edited:
@TDUBS However you can prevent the Stored Credentials page to return the actual password when someone tries to edit it by editing this file:
The function that returns the password begins on line 497. Preventing the function from returning the actual password should be enough if all you worry about is other admins that have access to Admin CP from accessing the password.
So this is the fix Jon would have to do in order to fix this problem?
@TDUBS It will only solve the issue that those users above reported. The issue where it's possible for other admins that have access to Admin CP to retrieve password of the stored credentials (and if you're not on an encrypted connection, it's also possible for MITM attacker to retrieve it though).
Last edited:
@TDUBS It will only solve the issue that those users above reported. The issue where it's possible for other admins that have access to Admin CP to retrieve password of the stored credentials (and if you're not on an encrypted connection, it's also possible for MIM attacker to retrieve it though).
I'll hold off on this then. Security through obscurity.
Last edited:
Also, it would be better if the add-on didn't return the actual FTP password on FTP Login Details option. And also the XenForo License Validation Token or even the XenForo License Key. For example, Audentio's UI.X has a better method. It won't return Audentio API key once it has been set. It only allows the user to change it, not view it. I'm not so concerned since I especially set the security setting of my admin.php on CloudFlare to High. And also the encryption of my whole forums is fully strict. But still, there's a concern since I'm not the only one who have access to Admin CP, and I can't tell for sure that the other admins' devices are safe.
Similar threads
- Replies
- 339
- Views
- 26K
- Replies
- 6
- Views
- 2K