I've been issue with this IP/Cloudflare headache for a while and finally got real visitor IPs working properly. It can cause breaks login for anyone on IPv6.
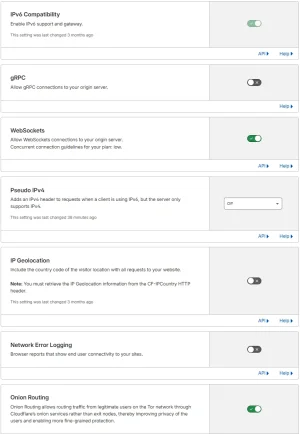
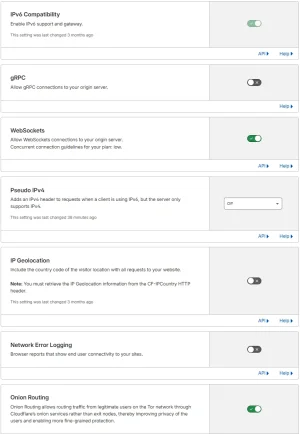
Here my CloudFlare Network settings:
Here is my own server:
Real IPs are CF-Connecting-IP header and mod_remoteip (or nginx real_ip that I have tested). Current visitors members shows correct IP.
The issue:
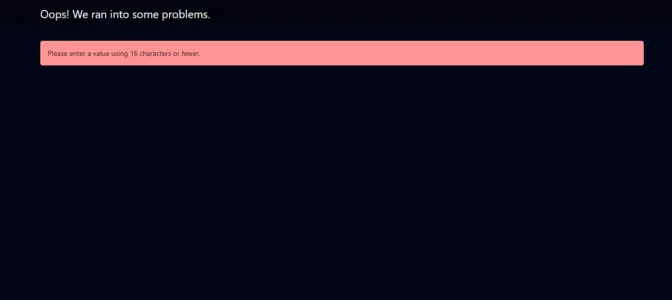
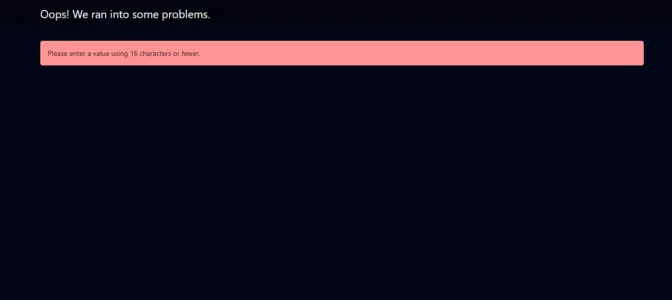
When Cloudflare Pseudo IPv4 is set to Off, may shows users on real IPv6 connections but when people tried to login and failed caused this:
A lot of people have reported that issue known caused by Pseudo IPv4 disabled/off at cloudflare. I have no clue but when pops up after submitting the login form (redirects to /login/login). IPv6 users can't log in at all. IPv4 users are completely fine. Fip Pseudo IPv4 to Overwrite Headers -> IPv6 gets mapped to short 250.xxx.xxx.xxx addresses, and login works perfectly again.
Important: This is isn't a passkey related. I have tested this on browser incognito mode and different browser (Edge, Opera, Chrome). I've tried cleared caches, rebuilt everything, no weird errors in logs, restarted NGINX, Apache service. Proxy passes the header cleanly. Also addons are currently disabled and still same the issue. Anyone there who have issue this with real IPv6 on normal logins? Is there some leftover IPv4 assumption somewhere in session/CSRF handling?
I would like to have run without Pseudo IPv4 overwrite headers if possible that can show real IPs would be nice.
Here my CloudFlare Network settings:
Here is my own server:
- XenForo 2.3.9 (latest version)
- Plesk at AlmaLinux backend with Apache & Nginx together
- Separate proxy server for VPS at CloudPanel and Nginx
- Cloudflare for proxy orange enabled
Real IPs are CF-Connecting-IP header and mod_remoteip (or nginx real_ip that I have tested). Current visitors members shows correct IP.
The issue:
When Cloudflare Pseudo IPv4 is set to Off, may shows users on real IPv6 connections but when people tried to login and failed caused this:
Oops! We ran into some problems.
Please enter a value using 16 characters or fewer.
A lot of people have reported that issue known caused by Pseudo IPv4 disabled/off at cloudflare. I have no clue but when pops up after submitting the login form (redirects to /login/login). IPv6 users can't log in at all. IPv4 users are completely fine. Fip Pseudo IPv4 to Overwrite Headers -> IPv6 gets mapped to short 250.xxx.xxx.xxx addresses, and login works perfectly again.
Important: This is isn't a passkey related. I have tested this on browser incognito mode and different browser (Edge, Opera, Chrome). I've tried cleared caches, rebuilt everything, no weird errors in logs, restarted NGINX, Apache service. Proxy passes the header cleanly. Also addons are currently disabled and still same the issue. Anyone there who have issue this with real IPv6 on normal logins? Is there some leftover IPv4 assumption somewhere in session/CSRF handling?
I would like to have run without Pseudo IPv4 overwrite headers if possible that can show real IPs would be nice.