I understand the same XF installation may require different kind of hashes depending on the authentication module used (e.g. vB imported users require MD5 whereas newly created XF users use SHA1 or SHA256).
As a consequence, in the login procedure, a user's password is transmitted in plaintext rather than as a hash. In comparison, vBulletin uses client-side Javascript to turn the password into a hash before sending it over the net, which seems somewhat safer to me (well, depending on the hash used).
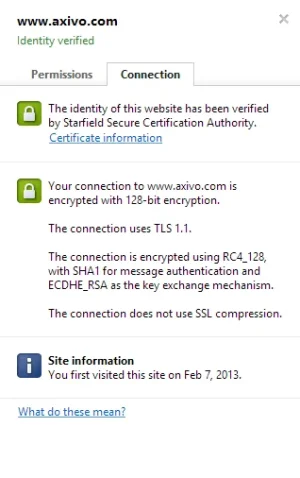
It's understandable that the password is transmitted in plaintext so that XF can keep the login procedure as flexible as possible. One way to solve this is to provide secure authentication over HTTPS.
Has anyone tried to use HTTPS conditional for XF login only?
Another way would be to provide several client-side generated hashes through Javascript (those that are potentially needed by the installed authentication modules) instead of the plaintext password, and have the respective authentication module pick the right one. The weak link would be the weakest hash (MD5 for example), but it's still better than plaintext. And it would make the authentication procedure less flexible in case a particular authentication module relies on acces to the plaintext password. Personally I would go with HTTPS since it is safer and would require less code hacking.
What do you think?
As a consequence, in the login procedure, a user's password is transmitted in plaintext rather than as a hash. In comparison, vBulletin uses client-side Javascript to turn the password into a hash before sending it over the net, which seems somewhat safer to me (well, depending on the hash used).
It's understandable that the password is transmitted in plaintext so that XF can keep the login procedure as flexible as possible. One way to solve this is to provide secure authentication over HTTPS.
Has anyone tried to use HTTPS conditional for XF login only?
Another way would be to provide several client-side generated hashes through Javascript (those that are potentially needed by the installed authentication modules) instead of the plaintext password, and have the respective authentication module pick the right one. The weak link would be the weakest hash (MD5 for example), but it's still better than plaintext. And it would make the authentication procedure less flexible in case a particular authentication module relies on acces to the plaintext password. Personally I would go with HTTPS since it is safer and would require less code hacking.
What do you think?