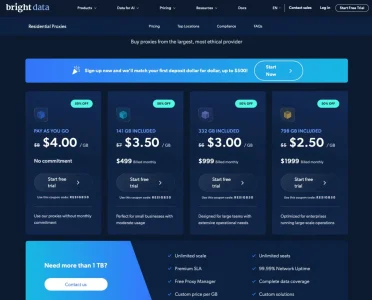
• scraping via residential proxies costs per GB of traffic and it is expensive (and often slow)
So my number 4 would be:
4.) poison the content. Send identified scrapers into a huge mess of false, halftrue or completely made up information and let they scrape it to poison the AI models that they are feeding, effectively rendering them useless. It is important to mix up true and false information and to have references linking to the true world to not make it too obvious. Also include huge pictures and graphics to make traffic expensive. On could create a repository for this stuff ("bogopedia") where people could have fun adding this kind of thing - could even be done using XenForo.
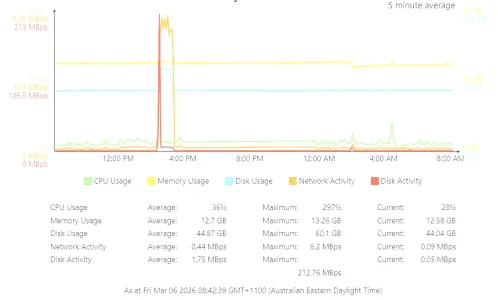
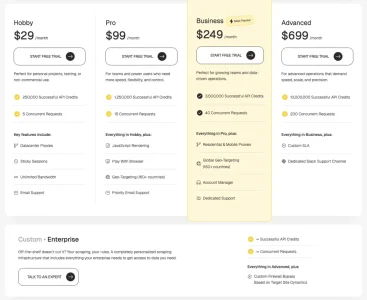
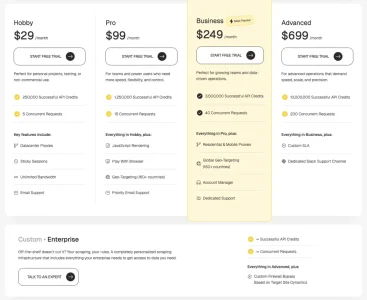
I stumbled upon the conditions of one of those services that rent out resident proxies and it seems indeed desirable to posion the requests with bogus content. Some of the proxy providers charge per GB of traffic, another charges per successful request and this is where it get's interesting:
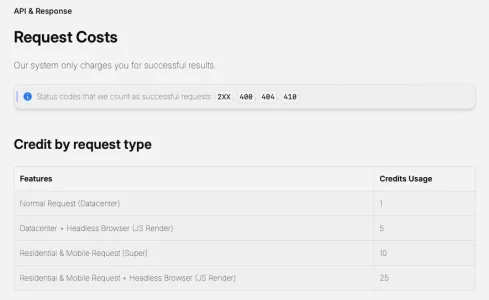
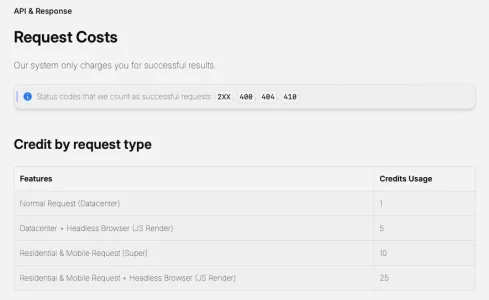
This means, a strict blocking via 403 won't cost the requestor anything, it would be better to redirect them to a bogus page or to present them at least with a 404 (like XF does if you lack sufficient rights to access the content you requested). The prices at said "service" seem relatively moderate, yet this quickly adds up as every request has to be paid and with 25 API credits per successful for residential proxies with headless and JS this adds up pretty quickly:
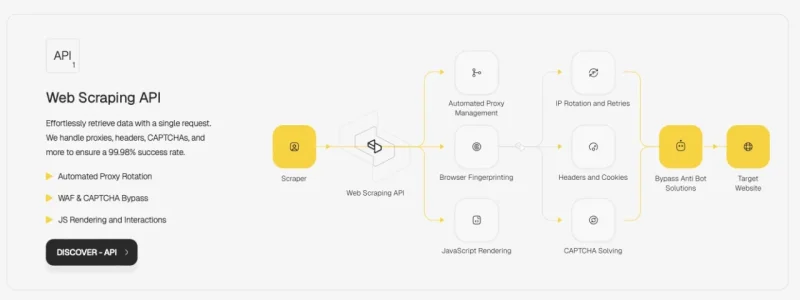
This is the architecture they promote and claim to have:
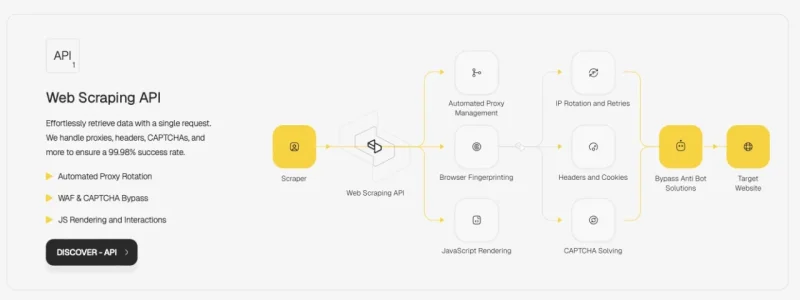
They also claim to have 110 million proxies and a success rate of 99,98%. As usual, you can believe this or rather not. ;-) As Usual, the company offering these services claims furiously that this all completely legal business, yet does not mention any name of someone working there or an address of the company but hides in whois behind a privacy protection service.
However, in this case it does not seem to be run by a company located in Cyprus, UAE, Dubai or Panama but in Wyoming - if the LLC that can be found on their webpage it true (which it seems to be). And with the name you can then find more information inc. a founder's name
as well as a company number and a legal address in the US
PACKEND, LLC American (Wyoming) company, Company number: 2021-001044605, Incorporation Date 18 de oct de 2021;, Address: 30 N Gould St Ste N Sheridan, WY 82801 USA

b2bhint.com
despite, according to the entry at crunchbase, the untertaking is based not in the US but in Ankara in Turkey.
Just in case someone wants to dive into a rabbit hole.