I've had a few people that use my Cloudflare add-on ask me what Cloudflare options/settings are best for XenForo. So rather than repeating myself privately, I'm going to turn this post into a bit of a configuration help document for those that want to read it.
Cloudflare is pretty great out of the box, but here's some things you can do if you feel it's beneficial to your site...
Protect yourself
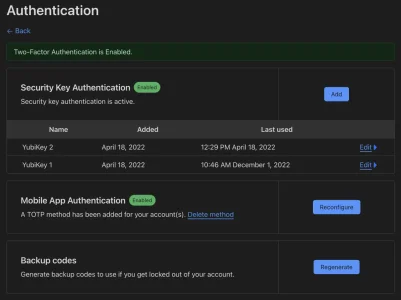
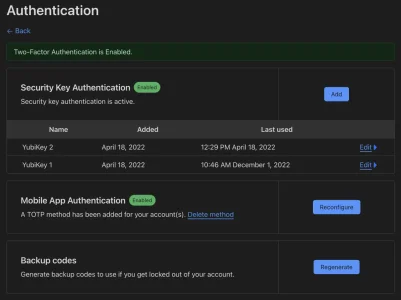
First things first, this goes for any important account you own, but it's worth repeating... Protect your Cloudflare account with two-factor authentication, ideally with a security key (also known as Passkey these days). If someone breaches your Cloudflare account, the amount of damage they can do is substantial (all your websites can go down, domains can be stolen in some cases, etc.)
Domain registrar
Cloudflare is a fully accredited registrar that can handle most domain extensions in one place. As a bonus, you aren't slammed with ads with them trying to upsell you with things like whois privacy (it's included for free) or hosting. They do registrar services for zero profit, so unless a registrar is offering domains at a loss, they will be the least expensive option.
 blog.cloudflare.com
blog.cloudflare.com
As an example, prices today for a couple domain extensions I personally use:
...you get the idea. Basically you can cut your domain registration costs in half (and get more).
Settings for a website/zone
Minimum TLS version: It's worth considering setting this to

 www.ghacks.net
www.ghacks.net
TLS 1.3: Turn this ON. Not sure why you would not want to support the latest version of TLS.
Firewall Rules: Use this to do things. Here are some ideas:
Auto Minify: JavaScript and CSS seem to be always be safe to allow with XenForo. HTML is like 99% okay in my experience (the only issue I've had with it was related to my own custom things I built on top of XenForo), but your mileage may vary.
Brotli: Turn this ON.
Early Hints: Turn this OFF. This can actually have a counter-productive effect where you are forcing users to load static resources like images and JavaScript (which XenForo has a lot of) on every page view even if they have it cached already in their browser.
Rocker Loader: Turn this OFF. Seriously, it's such a bad idea with XenForo.
AMP Real URL: Turn this ON. Not for the actual AMP URL, but it will add DNS CAA records for you automatically if you care about things like SSL Lab's SSL Report scores.
Cache Level: Make sure this is set to
Zero Trust: Use this to put an extra-level of protection on certain areas that only a limited number of user should have access to (
Page Rules:
HTTP/3 (with QUIC): Turn this ON. Allow end-users to benefit from the latest HTTP protocol improvements.
0-RTT Connection Resumption: Turn this ON.
IPv6 Compatibility: Turn this ON. This allows users to connect to your site and benefit from IPv6 even if your web server doesn't support IPv6 directly.
Other tricks you can do with Cloudflare
Cloudflare is pretty great out of the box, but here's some things you can do if you feel it's beneficial to your site...
Protect yourself
First things first, this goes for any important account you own, but it's worth repeating... Protect your Cloudflare account with two-factor authentication, ideally with a security key (also known as Passkey these days). If someone breaches your Cloudflare account, the amount of damage they can do is substantial (all your websites can go down, domains can be stolen in some cases, etc.)
Domain registrar
Cloudflare is a fully accredited registrar that can handle most domain extensions in one place. As a bonus, you aren't slammed with ads with them trying to upsell you with things like whois privacy (it's included for free) or hosting. They do registrar services for zero profit, so unless a registrar is offering domains at a loss, they will be the least expensive option.
Introducing Cloudflare Registrar: Domain Registration You Can Love
“I love my domain registrar.” Has anyone ever said this? From before Cloudflare even launched in September 2010, our early beta customers were literally begging us: "Will you please launch a registrar too?!"
The Cloudflare Registrar Promise said:From the price side it’s even simpler: we promise to never charge you anything more than the wholesale price each TLD charges. That’s true the first year, and it’s true every subsequent year. If you register your domain with Cloudflare Registrar you’ll always pay the wholesale price with no markup.
As an example, prices today for a couple domain extensions I personally use:
| Extension | Cloudflare cost | GoDaddy cost (doesn't include "protection" to keep domain from being stolen... that's $9.99 extra. wut?) |
|---|---|---|
| .com | $9.15 | $19.99 |
| .io | $33.00 | $62.99 |
...you get the idea. Basically you can cut your domain registration costs in half (and get more).
Settings for a website/zone
Minimum TLS version: It's worth considering setting this to
TLS 1.2. TLS 1.0 and 1.1 have weaknesses/vulnerabilities and were deprecated finally in 2020. Modern browsers have supported TLS 1.2 since 2013, so cutting support for TLS 1.0 and 1.1 is only affecting very edge users that are using browsers that are so old they can't get to any major website with it (websites like Google, Microsoft, Apple, Facebook, PayPal, etc. don't support TLS 1.0/1.1, so why should you?).
All major browsers drop TLS 1.0 and 1.1 in 2020 - gHacks Tech News
All major web browser makers announced on October 15, 2018 that the browsers that they produce will stop supporting the standards TLS 1.0 and TLS 1.1 in 2020.
TLS 1.3: Turn this ON. Not sure why you would not want to support the latest version of TLS.
Firewall Rules: Use this to do things. Here are some ideas:
- Block all access to internal directories (
internal_dataandsrcspecifically). - Force a challenge to bots that don't adhere to robots.txt based on their user agent.
Auto Minify: JavaScript and CSS seem to be always be safe to allow with XenForo. HTML is like 99% okay in my experience (the only issue I've had with it was related to my own custom things I built on top of XenForo), but your mileage may vary.
Brotli: Turn this ON.
Early Hints: Turn this OFF. This can actually have a counter-productive effect where you are forcing users to load static resources like images and JavaScript (which XenForo has a lot of) on every page view even if they have it cached already in their browser.
Rocker Loader: Turn this OFF. Seriously, it's such a bad idea with XenForo.
AMP Real URL: Turn this ON. Not for the actual AMP URL, but it will add DNS CAA records for you automatically if you care about things like SSL Lab's SSL Report scores.
Cache Level: Make sure this is set to
Standard. Anything else can cause problems for you with how XenForo's cache-breaking mechanism works when something is updated.Zero Trust: Use this to put an extra-level of protection on certain areas that only a limited number of user should have access to (
admin.php area and install directory).Page Rules:
- For a URL match of
*YourXenForoInstallation.com/css.php?css=*, give it a longBrowser Cache TTL, setCache Levelto "Cache Everything", give it a longEdge Cache TTLand enableOrigin Cache Control. This will allow XenForo's CSS to be cached in user's browser and the network edge. - You can do something similar for XenForo's proxied images, but if you do it, you lose the counter XenForo keeps for how many times proxied images are viewed by users. So if you care about that, don't do it.
- For sites that I allow users to use API keys, I do a HTTP Request Header Modification to turn Api-Key into XF-Api-Key. Nit-picky, but my users don't care that we use XenForo and it saves a few support issues where people ask what "XF-" means when they submit their API key in the request. You can automatically transform this with Cloudflare without needing to make any changes to XenForo.
- I do HTTP Response Header Modification to remove
expect-ct,nelandreport-toHTTP headers. I don't use them, so adding having 3 extra HTTP headers on each and every HTTP request just seems like a waste of network traffic to me.
HTTP/3 (with QUIC): Turn this ON. Allow end-users to benefit from the latest HTTP protocol improvements.
0-RTT Connection Resumption: Turn this ON.
IPv6 Compatibility: Turn this ON. This allows users to connect to your site and benefit from IPv6 even if your web server doesn't support IPv6 directly.
Other tricks you can do with Cloudflare
- Use Workers for your image proxy and URL proxy (doing this will give you a high-performance/free way to hide your server's IP address when it makes a request for images or URLs).
- Use R2 as a (much cheaper) drop-in replacement for AWS S3 for things like hosting attachments/images in the cloud.
Last edited:


