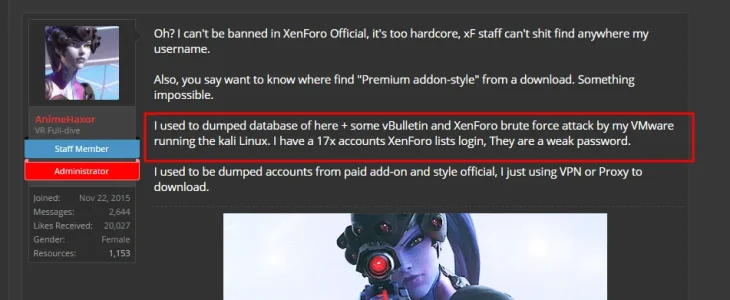
The registration form has a username validation function. it seems this can be abused by attackers to find out what accounts are present on the site. The attacker can run a script to try millions of possible usernames to get a member list. I have recently encountered such attack on my vbulletin big board, as vbulletin has a similar function. I've tried it out and there does not seem to be any limitation on xenforo registration either.
Once the attacker has a member list they are one step closer to hacking a site. Therefore I think it should be prevented.
This can be prevented by implementing a limit on this function, so that a user can only try X times, after which the user will be locked out from using this function.
Once the attacker has a member list they are one step closer to hacking a site. Therefore I think it should be prevented.
This can be prevented by implementing a limit on this function, so that a user can only try X times, after which the user will be locked out from using this function.
Upvote
21