Sim updated Geoblock Registration with a new update entry:
1.2.2 bugfix - assert admin permission
Read the rest of this update entry...
1.2.2 bugfix - assert admin permission
- Minor bugfix to explicitly enforce admin permissions on admincp tools
- updated icon
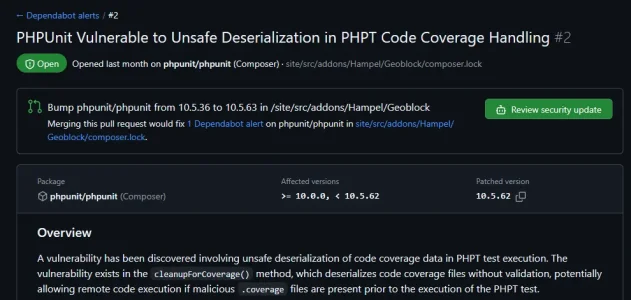
- latest composer dependencies
Read the rest of this update entry...