Code:
(
not http.cookie contains "xf_session="
and not http.cookie contains "xf_user="
)
and not cf.client.bot
I'm going to try the below one, as I think session is used for guests too, so just to exclude logged in users:
Code:
(not http.cookie contains "xf_user=" and not cf.client.bot)
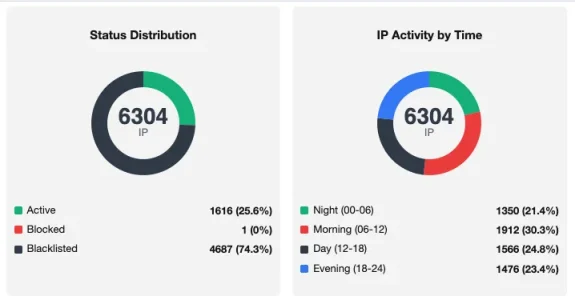
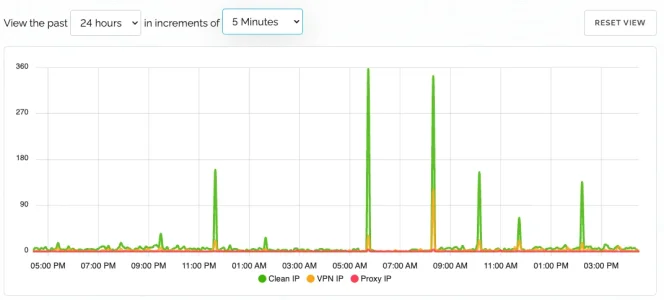
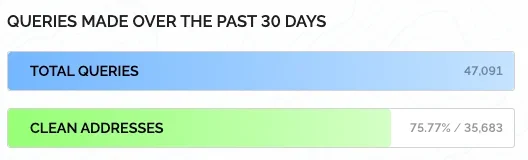
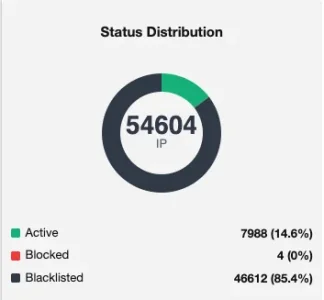
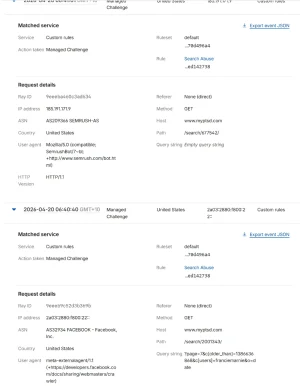
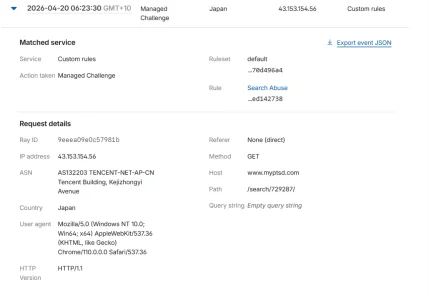
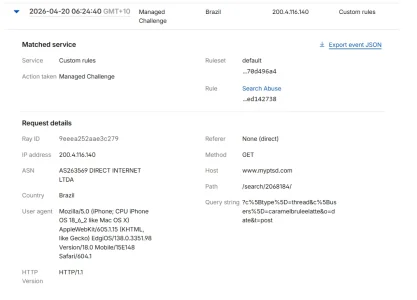
Managed Challenge. After it has been running for close to 24hrs, 1.5M events with only a 2k solve. I also have a prior rule for (cf.client.bot) to Skip managed rules, which was about 50k. Go into CF settings for the site, Security > Settings > Challenge Passenge and change the managed challenge time to like a day, so it doesn't upset anyone, but still stops everything non-human that one time.
Not sure if its totally correct, but its working. If there is an issue in the above, brains trust here will tell me. Took my proxycheck account down to a few dollars monthly.
View attachment 335759
Oh, and my server is locked down to only accept traffic via Cloudflare, no direct IP access other than my static IP I have.