Anthony Parsons
Well-known member
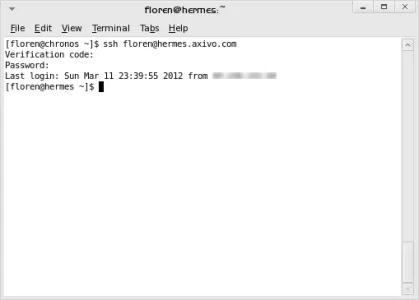
I was looking at my denied IP's today, having to fix a user who got caught due to unsuccessful login attempts. Looking at the list of attempted SSH logins, OMFG... China, Russia, Korea, etc etc. I assume hacking programs constantly sniffing the web for insecure logins?
I remember getting hosting years ago, where config firewall had to be asked for installation. Funnily enough, when I got my recent dedi via ServInt, config firewall came pre-installed and running this time around.
I remember getting hosting years ago, where config firewall had to be asked for installation. Funnily enough, when I got my recent dedi via ServInt, config firewall came pre-installed and running this time around.