kbarg
Member
Well one of my members on my Xenforo installation has an issue with someone or vice versa, they had decided to deface my website. After looking through my domain forwarders, dns', and like almost all the files on my forums server area. There are no changes, but index.php and any ex: (http://myxenforo.tld/members or http://myxenforo.tld/anything) all goes to their defacement, leading me to believe that my site was MySQL injected.
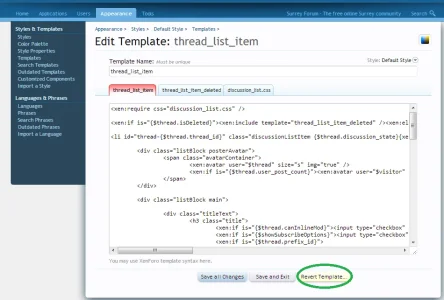
Assuming Xenforo might be like MyBB in a way, (no insult intended, MyBB themes use database.). What if any XML files are incorporated into the MySQL database? That is the only solution I can see.
Is there a way I can see what was my last SQL table updated, or where my XML files are located (partials) if possible on the MySQL database, so I can fix my site.
Assuming Xenforo might be like MyBB in a way, (no insult intended, MyBB themes use database.). What if any XML files are incorporated into the MySQL database? That is the only solution I can see.
Is there a way I can see what was my last SQL table updated, or where my XML files are located (partials) if possible on the MySQL database, so I can fix my site.